Redefining Intrusion Detection: From Static Signatures to Context-Aware AI Agents
Introduction: The Evolution of Network Security
For decades, intrusion detection systems (IDS) relied on a straightforward method: compare network traffic against a database of known attack signatures. This approach, known as signature-based detection, was effective against predictable threats but struggled with novel or carefully disguised attacks. Today, the rise of machine learning, and in particular the emergence of SnortML and agentic AI, is transforming the very architecture of intrusion detection. The central question is no longer "Does this packet match a known pattern?" but rather "Does this traffic make sense in its broader context?" This shift marks a fundamental change in how we think about security monitoring.
The Limitations of Traditional Signature-Based Detection
Signature-based detection works by comparing incoming traffic against a set of predefined rules or signatures. Each signature corresponds to a known malicious pattern—for example, a specific byte sequence in a worm payload or a unique command used by malware. While this method is fast and reliable when the threat is known, it suffers from several critical drawbacks:
- Zero-day blind spots: New or modified attacks that don't match any signature go unnoticed.
- Context ignorance: A signature might trigger on a legitimate but slightly unusual packet, causing false positives, while a truly malicious pattern hidden in normal traffic might evade detection.
- Maintenance burden: Security teams must constantly update signature databases, a process that lags behind attackers' evolution.
As network environments become more dynamic and encrypted, these limitations grow more severe. The need for a smarter, adaptive approach has become critical.
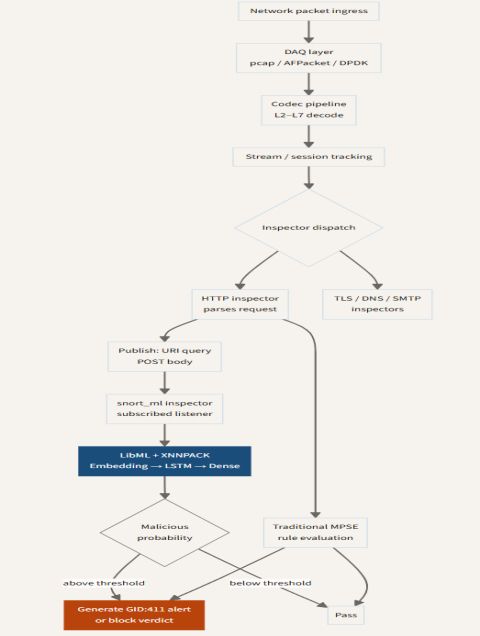
Enter SnortML: Machine Learning for Deeper Insight
One of the most promising developments in this space is SnortML, a machine learning extension for the widely used Snort intrusion detection engine. Rather than relying solely on static signatures, SnortML introduces statistical models that learn the normal behavior of a network over time. When traffic deviates from that baseline—even if it doesn't match any known signature—it can flag the activity for further investigation.
SnortML employs techniques such as anomaly detection and classification. For example, it can analyze packet timing, payload entropy, or flow patterns to identify behavior that is statistically unlikely under normal conditions. This capability is especially valuable for detecting:
- Slow, low-volume data exfiltration
- Encrypted tunnels used by command-and-control (C2) traffic
- Zero-day exploits that don't produce signature-matching byte sequences
By shifting the question from "Does this match a pattern?" to "Does this behave normally?", SnortML reduces false positives and catches attacks that signature-based systems miss. However, machine learning alone is not enough—it still requires human analysts to interpret alerts and decide on responses.
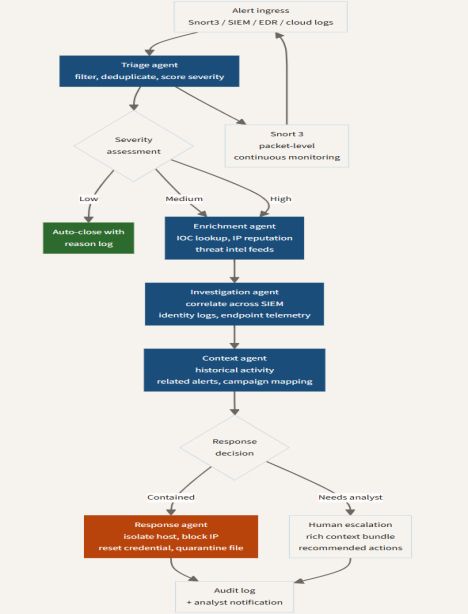
Agentic AI: Autonomous Decision-Making at the Edge
The next evolutionary step is agentic AI—autonomous software agents that not only detect anomalies but also act on them in real time. Unlike traditional ML models that output a score or label, an agentic AI system can reason about the context, formulate a response, and execute it without human intervention. This capability is transforming intrusion detection from a passive monitoring tool into an active defense system.
Agentic AI in IDS typically follows a loop:
- Observe: Continuously collect traffic data and analyze it through multiple lenses (signatures, ML models, behavioral baselines).
- Orient: Combine all sensor inputs to understand the full picture—for instance, correlating a spike in DNS queries from a single host with a recent phishing email.
- Decide: Evaluate possible actions (block the traffic, isolate the host, log for later review) based on risk, policy, and potential impact.
- Act: Execute the chosen action automatically, often within milliseconds.
This level of autonomy is crucial for defending against fast-moving threats like ransomware or worm outbreaks, where every second of manual deliberation gives the attacker an advantage. Moreover, agentic AI can adapt its own detection strategies over time through reinforcement learning, becoming more effective as it encounters new scenarios.
Architectural Implications: From Centralized to Distributed
The shift toward ML and agentic AI is also driving changes in intrusion detection architecture. Traditional IDS were centralized: all traffic was funneled to a single appliance or server where signature matching took place. This model created a bottleneck and a single point of failure. With SnortML and agentic agents, processing can be distributed across the network—on switches, routers, firewalls, and even endpoint devices.
Consider an agent deployed at the edge of a corporate network. It monitors traffic locally, applies lightweight ML models, and communicates with a central coordinator only when it needs to escalate a decision or share intelligence. This federated approach reduces latency, scales more easily, and improves resilience. If the central system is compromised, edge agents can continue to operate independently.
Furthermore, these agents can share knowledge with each other via secure peer-to-peer channels, enabling a collaborative defense without relying on a single authoritative database. This is a fundamental departure from the client-server model of signature-based systems.
Challenges and Considerations
While the promise is tremendous, deploying SnortML and agentic AI in real networks comes with hurdles:
- False positives from ML models: Anomalous but benign events (e.g., a large software update) can be misclassified if the training data is not representative.
- Explainability: Security teams need to understand why an agent blocked a connection; black-box models are difficult to audit.
- Adversarial attacks: Attackers may attempt to poison ML training data or craft inputs that deceive the agent's decision-making.
- Governance: Autonomous action raises questions about accountability—if an agent mistakenly blocks critical business traffic, who is responsible?
These challenges are active areas of research. Many organizations choose a hybrid approach, using SnortML for detection while keeping human-in-the-loop for high‑stakes actions.
The Future: Self-Healing Networks
Looking ahead, the ultimate goal of this evolution is the self-healing network: a system where sensors think, agents act, and the entire security posture adapts automatically to changing threats. SnortML and agentic AI are foundational technologies for reaching that vision. As they mature, we can expect intrusion detection to become less about watching and more about intelligent, autonomous response.
In summary, the question is no longer just about pattern matching. It's about understanding context, reasoning over data, and taking swift, appropriate action. The sensor has started to think—and the network is becoming smarter because of it.